The discussion centers on Advanced Internet Solution 2087193276, outlining a modular architecture that separates perception, processing, and communication. It emphasizes interoperable interfaces, scalable deployment, and coherent verification for autonomy and resilience. The security stance favors continuous assessment and adaptive response. Real-world rollout covers modular integration, disruption-minimizing migration, and metrics-driven progress. A phased roadmap ties assessment to deployment with rollback plans, while balancing latency, reliability, and traceability, inviting scrutiny on how these elements evolve together.
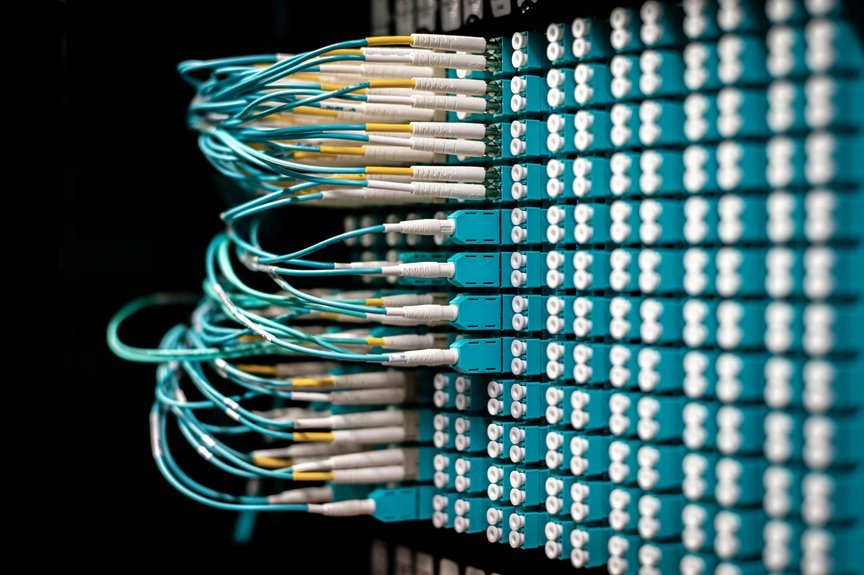
Core Architecture and Networking Principles
The core architecture of an advanced internet solution rests on a modular, layered model that separates concerns across perception, processing, and communication. It emphasizes interoperability and scalability through a clear network topology framework and disciplined protocol efficiency. Components function with defined interfaces, enabling flexible deployment, straightforward maintenance, and targeted optimization. This structure supports autonomy, resilience, and freedom to innovate within a coherent, verifiable system.
Security Posture and Threat Adaptation in Practice
Security posture in practice centers on continuous assessment, layered defense, and adaptive response, ensuring adversarial activity is detected, contained, and recovered from with minimal disruption. The approach emphasizes resilience, proactive monitoring, and disciplined incident handling. Security posture informs risk prioritization, while threat adaptation enables timely adjustments to controls, configurations, and workflows—maintaining balance between openness and protection within the evolving threat landscape.
Real-World Implementation: Integration, Migration, and Metrics
How do organizations translate strategy into practice when integrating, migrating, and measuring outcomes across complex environments? Real-world implementation unfolds as a disciplined sequence: architecture patterns enable modular integration, migration plans minimize disruption, and metrics quantify progress. Cross-functional governance aligns teams, while latency optimization and continuous validation ensure performance. Documentation, traceability, and disciplined rollback preserve freedom within structure and accountability across platforms.
Roadmap to Action: From Assessment to Deployment and Ongoing Optimization
Roadmapping the journey from assessment to deployment and ongoing optimization requires a disciplined sequence of actions. The process defines objectives, inventories capabilities, and maps risks, then selects scalable architectures.
Deployment follows with phased testing, rollback plans, and metrics.
Ongoing optimization emphasizes monitoring and feedback loops, balancing scalability tradeoffs and latency budgeting to preserve performance, reliability, and freedom of operation.
Conclusion
The architecture, security, and implementation framework cohere into a disciplined, modular system that adapts with purpose. By separating perception, processing, and communication, it remains interoperable and scalable, while continuous risk assessment guides adaptive responses. Real-world migration is deliberate and measured, anchored by metrics and rollback plans. From assessment to deployment and ongoing optimization, progress follows a steady drumbeat—precision in execution, resilience in operation, and a future-ready stance that keeps pace with evolving platforms.