Crypto replaces trusted intermediaries by encoding trust, rules, and verification into programmable networks. Distributed consensus and smart contracts automate settlement, governance, and enforcement without a central arbiter. Verifiable credentials and decentralized identifiers empower user sovereignty, while cryptographic proofs validate legitimacy and reduce counterparty risk. Tokenized liquidity speeds settlement and lowers costs, but governance, security, and regulation impose trade-offs between openness and control. The question remains: can these systems scale securely enough to rival legacy intermediaries, or will friction shift to oversight and architecture choices?
What “Third Parties” Do in Traditional Transactions
In traditional transactions, third parties perform essential coordination and verification functions that individuals cannot reliably execute alone. They assess credibility, enforce rules, and arbitrate disputes, mediating risk and information asymmetry.
Middlemen aggregate liquidity, authenticate identity, and route assets, multiplying costs but reducing friction.
Third parties provide reliability scaffolding in markets, enabling scalable exchange while shaping governance, compliance, and trust frameworks for participants seeking freedom within constraint.
How Crypto Removes Middlemen Through Trustless Tech
Crypto removes middlemen by replacing centralized trust with programmable, verifiable rules executed by code. Trustless infrastructure enables autonomous verification without intermediaries, reducing counterparty risk and processing time. Distributed consensus aligns network participants on state, ensuring integrity with minimal oversight.
Measurable gains include lower fees, higher throughput, and resilient fault tolerance; risks center on code quality, governance, and exploitation windows.
Freedom objectives hinge on openness, auditability, and optional participation.
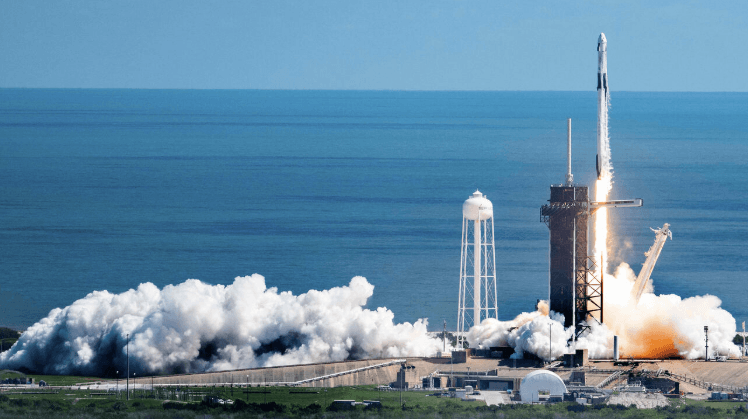
See also: Private Space Companies Rising
Use Cases: From Payments to Smart Contracts
The evolution from trustless, code-governed interactions to concrete use cases is evidenced by a spectrum ranging from payments to programmable contracts.
In practice, payments optimize settlement speed and reduce intermediaries, while smart contracts automate compliance and escrow.
Decentralized identifiers enable user sovereignty, and verifiable credentials enhance identity assurance, enabling scalable, auditable, trust-minimized interactions without central authorities.
Risks, Trade-Offs, and How to Evaluate Crypto-Enabled Solutions
Are the benefits of crypto-enabled systems worth the accompanying risks and trade-offs? The analysis identifies measurable costs and uncertainties: compliance costs rise with jurisdictional demands, while regulatory uncertainty creates strategic delays and redesigns. Trade-offs include security versus convenience and centralization versus permissionless structures. Evaluation relies on risk-adjusted ROI, security audits, interoperability metrics, and ongoing governance frameworks to balance freedom with due diligence.
Frequently Asked Questions
How Do Crypto Fees Compare to Traditional Intermediaries?
Crypto transaction fees generally vary; they can be lower or higher than traditional intermediaries, depending on network congestion and fee models. In speed comparisons, on-chain settlements may lag, while some layers offer faster options with variable transaction fees.
Can Crypto Eliminate All Forms of Middlemen?
Crypto cannot eliminate all middlemen; distributed identity and permissioned networks reduce intermediaries but not entirely. Analysis suggests efficiency gains and risk tradeoffs, quantified by lower switching costs and governance overhead, revealing residual roles for trusted institutions in complex, regulated ecosystems.
What Governs Trust in Trustless Systems?
Trust in trustless systems hinges on defined trust assumptions, rigorous risk management, robust governance models, and aligned system incentives; governance transparency, empirical audits, and incentive design collectively quantify reliability and empower a freedom-seeking audience.
Are There Regulatory Risks With Crypto-Enabled Solutions?
Regulatory risks exist with crypto-enabled solutions, including evolving compliance mandates and enforcement uncertainty. Decentralized governance and on chain privacy shape risk exposure, influencing audits, reporting, and operational controls in a pragmatic, quantitative analysis for freedom-seeking audiences.
How Scalable Are Blockchain-Based Transaction Networks?
Surprisingly, blockchain networks exhibit limited scalability; they face scalability constraints and modest network throughput. Analytically, throughput plateaus as blocks and consensus rounds grow, demanding optimization, sharding, or layer-two solutions to sustain practical transaction volumes for freedom-seeking ecosystems.
Conclusion
In traditional exchanges, intermediaries coordinate trust and enforce rules; crypto replaces these functions with programmable, verifiable systems. Quantitatively, settlement can be faster, cheaper, and more auditable, while risk is redistributed toward cryptographic security and governance design. Yet trade-offs persist: regulatory clarity, security discipline, and decentralization tension shape outcomes. As the adage goes, “trust, but verify”—and with crypto, verification becomes algorithmic, enabling evidence-based evaluation of cost, latency, and resilience across each solution.